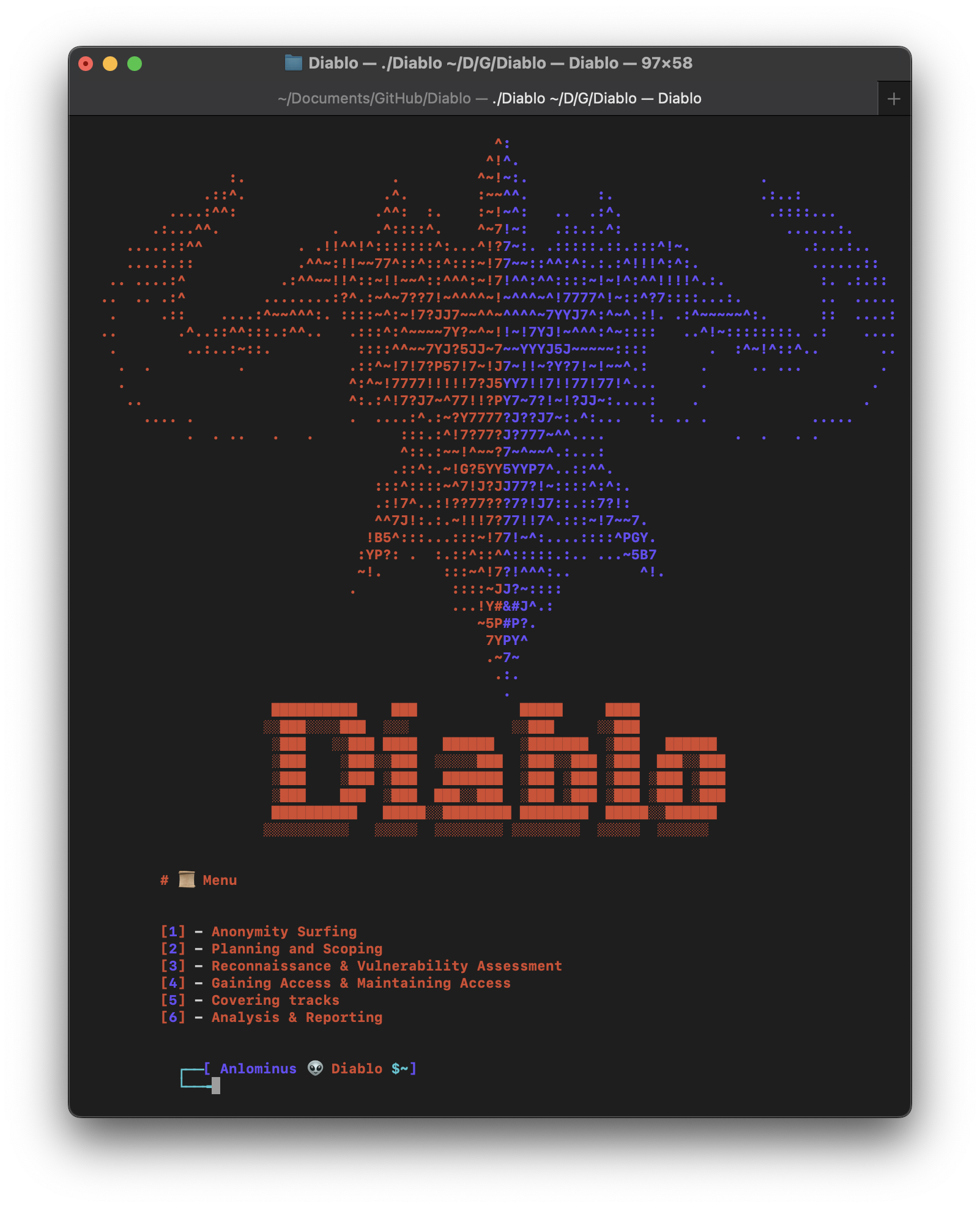
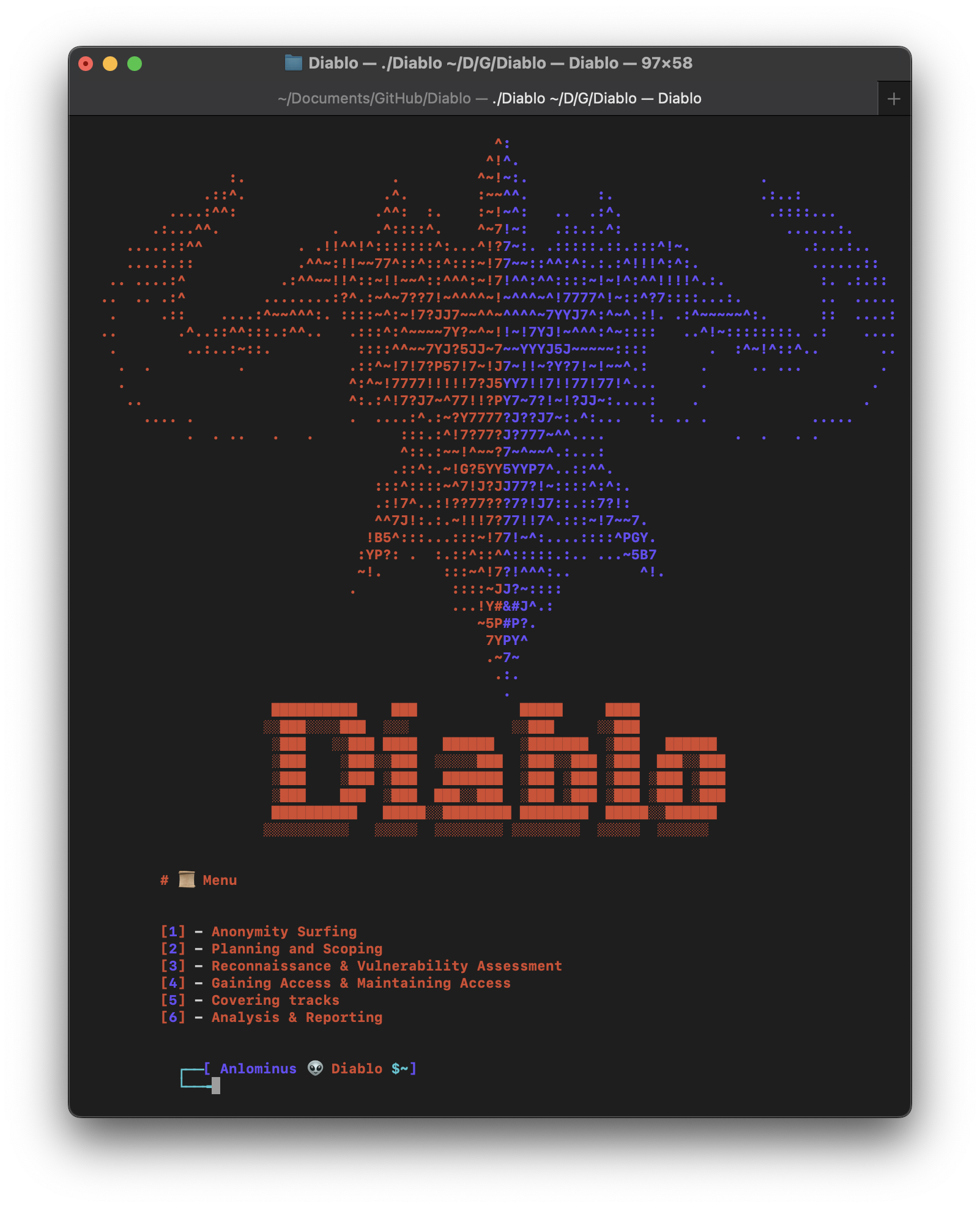
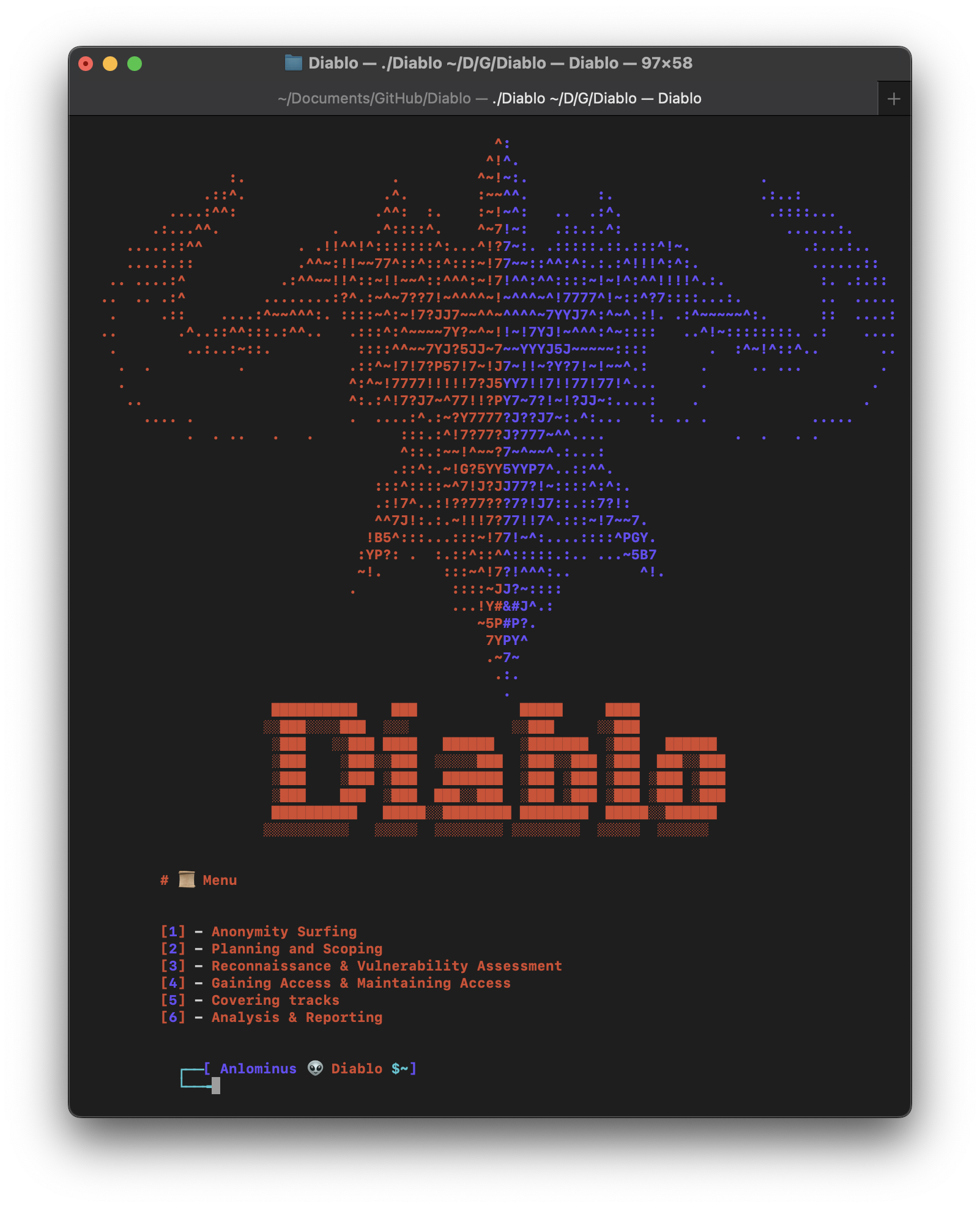
# [Diablo](https://github.com/Anlominus/Diablo)
Diablo ~ Hacking / Pentesting Tools